Privacy and Safety of NB-IoT Devices
Show transcript [en]
okay so uh hello everybody and uh thank you uh for your time and this is ali and uh i really happy to be here at great besides barcelona conference and today i'm gonna talking about uh some aspects security aspects of uh internet of things especially narrowband internet of things uh based on llc communication so i think it is interesting for you and uh so let me going to slide show
okay so first of all this is ali and uh as mentioned before i i have almost nine years of experience different variety of security fields and also i'm a regular inspector and trainer at many international conferences and real i really love to play with beats and bias and signal and radio and uh before start let me switch to shows automatic show okay
uh what is in terms of things maybe most of you heard about there are some uh special components of internet of things uh like uh some hardware they're acting as sensors uh and also there are some medievars and apis maybe and there there are some gateways as well as some integration with the web application and maybe mobile application uh for management purposes and uh another thing is that uh we may hear about internet of things and uh such a technologies in different uh businesses and purposes like industrial internet of things which is very uh interesting nowadays uh the second one then one of the most critical one is healthcare in healthcare um actually healthcare industry uh taking
advantage of internet of things as well as uh all kind of mobile communication and uh actually telecom based infrastructure uh actually for uh connectivity for better uh connection speed and the less delay and latency and there are many medical devices and sensors all around the world acting as uh internet of things a sensor and um the main advantage of internet of thing is that connecting every sensors every hardware and software together with a great and portable and flexible management so the next one is smart city uh so different uh sections uh playing uh critical roles uh in smart city and uh most of connection is based on internet of things and also smart home maybe you're facing with a smart home
technologies they're taking advantage of internet of things as well and other uh relative industries like agriculture uh so there are many solutions uh actually uh working in agriculture based on internet of things and nb iot and narrowband internet of things as well so for example uh if we want to detect fire we can take advantage of internet of things technologies or even uh have better actually uh performance uh and less uh water wasting we can take advantage of internet of things and nba iot in agriculture industry as well so uh actually uh i want to uh go deeper inside narrowband internet of things so first of all i want to talk about uh another aspect called ltm
or actually lte machine type communication or ltmtc uh it's based on even technology developed by the international standards organization 2gpp and it's enabled all kind of hardware and sensors devices and equipment in the field of internet of things and related services for iot service and applications so actually uh ltm uh allows the reuse of lc installed based on a great coverage and uh what is nvit as i said before it's narrowband iot it's a radio based technology uh with set up over cellular communication which is uh specially uh prepared for indoor coverage a long battery life a great volume of equipment uh user equipments and devices with a low cost of uh deployments actually uh nbit
limits bandwidths uh to a single narrow band of approximately 200 kilohertz uh and offering get greater speeds of uh actually 26 kilobytes in a really in 13 release of the international standard 3gpp and there are some other uh version of mbiot developed by 3gpp also and actually uh ltm and nbiot are together and their uh complementary solutions so [Music] scientists and researchers think about that uh internet of thing is very useful for different kind of industry people and experts all around the world so what is the better uh solution to take advantage of this great technology so actually the main issue in internet of things is the infrastructure and the network connection so what is the best network connectivity
all around the world with the greatest uh coverage and less latency and delay with low cost so absolutely there it is uh cellular based communication or mobile network communication so companies and uh international organization try to integrate internet of things with cellular communication and it is right now it is mbiot it's based on a cellular communication especially in fourth generation in lte and it's actually taking advantage of uh radio section or radio access network in lte which is called eu trend evolved utran and uh there are many uh advantage uh between nb iot and iot because we have more speed more security feature uh however in this slot in this presentation i'm going to talk about more about some
issues regarding nb iot especially as i mentioned before because the infrastructure is based on lte communication and radio based communication in lt generation uh we're going deep to uh review how a hacker and antaker would take advantage of some issues to exploit and what kind of vulnerabilities are in place in this industry so first of all i'm going uh to have a little introduction about our privacy in lte communication actually uh um so and to be honest uh most of mobile operators use uh some kind of dedicated spectrum bands uh uh under provision of license granted by their for example national regulator or other organization so m or mobile network operator uh provide connectivity using a standard
network technologies like umps gsm and lte and 5g nowadays as specified by some global organization like 3gpp the two major uh mobile iot technologies ltm and narrowband iots standards by 3gpp uh are funded by large number of mobile operator and supplier of equipment actually allowing the ecosystem to benefit from economic upscale and low cost of development and deployment you know and the security specification of narrowband internet of things are close to those of standard standards in iot but there are several variations uh primarily with regard to low energy iot hardware network connectivity etc and the iot terminal device typically has powerful processing capacity and the complex network communication protocol and a higher security reinforcement strategy
and typically power consumption is high and regular charging is important and low cover iot system on the other hand are distinguished by uh actually vulnerabilities are more likely to pose a threat to terminals in addition um actually the state of denial of service denial of service attacks may be triggered by basic resource use in comparison actually the number of low power consumption iot terminal system i'm in is much higher in real implementation than in conventional iot internet of things devices so uh actually even greater security will result from some minor security risks and uh india iot is centralized systems such as lte where uh basis station actually we called base station in lte we called in e-node b manage both
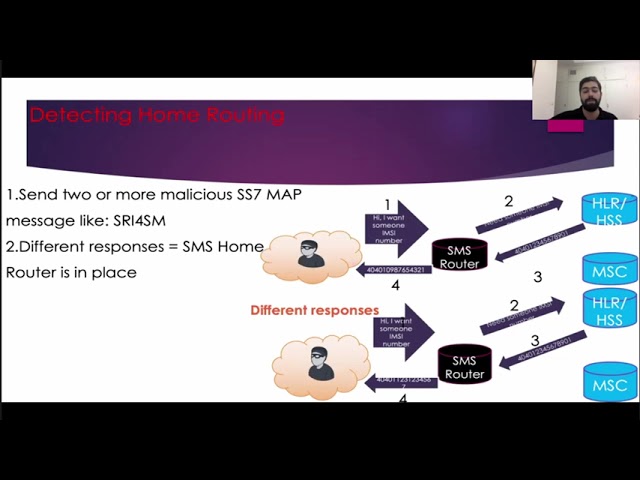
uh uplink and downlink scheduling um to ensure the synchronization of resources between systems uh and as you can see uh billion of connected devices can and subscribers user user equipment uh connecting to the basic station to take advantage of uh lt infrastructure and they are acting as anviolitis sensors and so to be concluded actually this infrastructure is some kind of critical infrastructure in portrayal industry so actually here we have example but before that i want to a little uh talk about the example and this security aspect in this slide so um actually uh searchers can impersonate cell phone users by uh as you know leveraging a flaw in the mobile communication protocol in lte or maybe
in traditional technologies like ss7 uh in past generations like gsm and 3g therefore through the cell phone bill uh they will look fee-based service under their name and are paid for for example an attacker may book facilities stream screens but the owner of the attack phone would have to pay for them you know uh actually there are some other kind of tanks uh regarding uh the infrastructure the telecom infrastructures is draw in denial of service uh actual location tracking etc so and now in this case due to the existing of vulnerabilities and extensive security of actual privacy security uh and design authentication processes in mobile networks so the design uh actually the design and implementation
of these algorithms in the third and fourth generation lte uh has been greatly improved than gsm technology so uh actually there is an advanced mutual authentication mechanism and encryption as well in lte network and this has reduced security risk but it should be noted that security concerns uh actually have not yet been fully addressed and reasons for this include the vulnerability of this technology to attacks such as as i said location tracking fake bts and lte fake enough b implementation or rogue it would be using protocol exploitation and based on the research and experiment performed uh as uh based on this example uh actually uh on a it's it's somehow a real network or in a test bed it's possible to perform
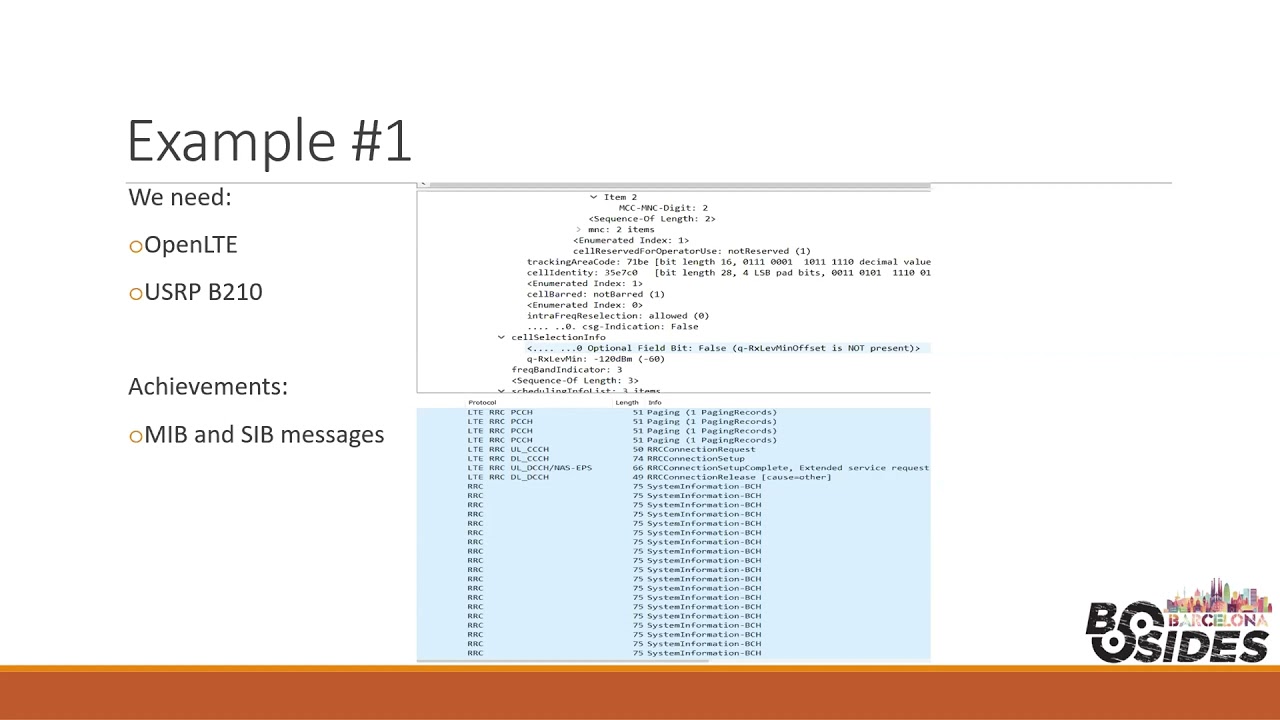
this kind of research and experiment uh actually which performed in lte protocol especially in access layer in radioactive network and actually you can see uh you you i used a radio capture in lte utran without any special access to the network and in this protocol uh despite security mechanisms such as encryption and mutual authentication is vulnerable to protocol exploitation and set up a fake uh basis station or regular node b uh an attacker can use uh this to sniff on traffic with a sim card or software defined radio for sdr so actually a number of exploits are found and introduced based on open source version of lts stack open lte as i mentioned and mainly focused on the lts
stack open source implementation analysis is actually given on the growth of low cost indicator and exploits that trigger blocking of mobile devices which were first introduced globally uh in many events and uh research communities and so all traffic and data are collected uh and captured by a usrp b2010 and baseband by using uh these features uh we will be able to capture and analyze data in physical layer as you can see based on the wireshark results in this slide such as are receiving real-time information decoding the non-access stratum uh or steep oracle and system messages in nlp and the information gathered during the research is collected from a real uh uh actually function which i emulated in
open source environments and the sniffer system acted as enzy catcher in this research and capture the emc number which is the most valuable information and it is unique for every mobile subscriber all around the world so uh it's something like a static ip address which is unique for you so this is important for a hacker or attacker to have your static and permanent address so amz is acting like that so it is very important and actually we capture the emcee of active subscribers or maybe emulated subscribers in the area and the the analysis was performed with open lt uh an srs lt as well software in order to listen to traffic and implement you know to be
uh actually in emulation environment and all that exchange between the user equipment i mean that the mobile phone and the basis station is intercepted but only actually control plane traffic actually that includes signaling data is important to us and this section examines the exploitation of the lt protocol using the analysis of the collected signaling data and a number of security aspects and abuse of lt protocol uh mentioned before and the most uh spotlight of which that are extraction of information from mib and sib messages and the denial of service attack for the os and location tracking using the implementation of rogue inaudible and this um simplifies the user equipment's initial access protocol and uh so but it could
potentially be leveraged by an attacker to create for example sophisticated jamming attacks customize configuration of arugula base station or attuning other sophisticated attack and complex attacking scenarios so based on the pictures here uh there are some contents of my sib messages in voice are transmitted by a commercial enough to be uh in my test area from the information extracted from these messages and then seeker can discover the mobile operator that operates that cell the tracking area code received power threshold to trigger a handoff and adjust cell and a series of configuration data could be influenced to set up a fake base station so and one of the most valuable segments of information from the protocol exploit
point of view uh actually is the list of uh high priority frequencies uh these parameters can be configured on a regular you know db it activate most user equipment and mobile phones to attach to that malicious base station in addition an attacker can also extract mapping of important control channels on a physical layer from the sib messages and this can be leveraged can we configure a smart jammer so and also open lc provides a traffic lock feature can be executed to pass it with scan broadcast information from the nearby base station a low cost alternative can be implemented on rtl str radio running the lte cell scanner tools so actually uh based on pictures neighbor cells that successfully
detected by tool and the decoded information of both mib and sib messages can be shown here and uh here tmz capture and actually in order to implement and exploit this attack uh it is necessary to capture subscriber nz on air uh so interesting the point here is that that a low volume of emzy values is exchanged between user equipments and the network due to its very high importance as i mentioned before uh mcnumber and sometimes this exchange supervisors under some situations as a when descending attach network as you can see here at that stage actually mobile phone uh or user equipment sends the mz uh before authentication and nas protocol which handling authentication and other related procedures
and now the attacker disconnect the subscriber and implement arugula noteb or fake one so that all subscribers in that specific area to send their emc number toward the attack station so uh it's that's great eric inaudible is a fake base station that is illegally set up uh on the lt network and operated by a hacker or an attacker by a open source software framework uh which are widely available on the internet and based on the picture uh simple subscriber attach request in wireshark uh can be seen and the subscriber has sent attach request message along with a related clear text mz number uh to authenticate and complete the connection process to the network so if
arugula node b has been set up with a required inode network promoter the attacker can now launch a potential serious threat such as man in the middle attacks denial of service analysis messages or inject as some kind of malicious messages to the attachment process or deny user equipment mobile service and downgrade to a non-lte network so this the mbiology sensor will then downgrade to a non-lte like umtsn 2g which is a great environment for a hacker moreover denial of service attack uh actually that may lead to network failure or downgrading to non-healthy a network or refusing all left for access so okay i'm going more fast and the exploitation actually uh based on my previous uh explanation
here uh is another exploitation it's some kind of active exploitation and the hacker trying to actually play btau or traffic area update reject message which require no security keys and the regular you know we could target any lte mobile user in its area for provisional denial of service it doesn't matter it's a nvtr nb iot sensor or a real subscriber you know uh and a similar thread is also possible for service reject or attach which you reject require messages actually or request on responses in the network uh whenever the user equipment transmits a tau request message to a regular node b it would be still be actually associated to the real network and this message is also
integrity protected but not encrypted under the nas security context and this will be a pretty uh an opportunity for attacker who could easily decode and send respond with a ta reject message and so uh and that does not require the integrity enforcement as well so actually based on the picture user equipment and nbit sensor actually will accept the reject cause and continue to act further by deleting all existing service connected to the actual network and in addition tiu statutory requests will not be searched for uh for or sent by the user equipment or sensor to any nearby legitimate lte network uh causing temporary denial of service uh with less effect and uh as you can see
some other kind of similar attacks and vulnerability are possible in lte network and right now due to lack of time uh i should go into conclusion and uh i think my time is over right now and thank you everybody uh for your time thank you besides uh have a nice day if there is any question i'm here to answer questions thank you yeah thanks ali uh yeah let's wait uh a little bit over time let's wait a couple of minutes it's someone from the audience here in zoom or someone in the youtube channel wants to write us a question um i have a question actually um again this is not my expertise so it was really interesting and i know
that it's a huge like there is a word right behind it but then a question is it possible would it be possible to apologize to um they take an i i s an imc catcher and it would be possible i mean me as a user of a device could i have like a nap or something that say hey so i mean be careful that someone is catching these things is it possible yes actually uh there are many incidents uh on the news that maybe uh some organization found easy catcher devices because there are many commercial indicator devices all around the world and for different purposes but it is possible to build and run your own inc
catcher based on open source tools and you need some kind of a platform and uh to actually emulate this stack like open lte srslt and uh software defined radio like usrp or blade rf hack rf or rtl str uh whenever you want to focus on a specific uh cellular network generation it's different to use uh which one which kind of actually str you want to use it's based on the specification and your requirements and on and on the user side or so let's say uh i have like you know can i detect if someone has created an nc capture i mean do i know if someone is actually it it's really it's it's really tough
because uh we we as a subscriber normal subscribers cannot detect the amc catcher or lugo and not be in a different network however mobile network owner and operator all around the world uh facing with this kind of issues they cannot detect such uh issues and fake basis station but uh some groups and also uh me uh worked on some solutions to detect the fake stations based on some behavior analysis and machine learning algorithms uh to detect a fake base station in earlier stages okay oh that's awesome okay so we don't have questions so far but i would love if you can send these research documents in the uh hallway chat uh in slack right because i definitely want to zoom in and
look at the data um we don't have any question now here so if someone has any questions you can just go in slack sagrada familia channel or the hallway channel you can write those questions there ali and myself would be making sure that those are addressed um again thank you very much ali and thanks for joining us it was really interesting thank you